In this article, we will look at how to solve the problem of syncing passwords from on-premises Active Directory to Azure via Azure AD Connect.
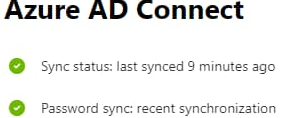
Azure AD Connect synchronizes passwords between on-premises ADDS and Azure AD every 2 minutes if you use Password Hash Synchronization (PHS).
The ADSync and ADSyncDiagnostics PowerShell modules are installed when you deploy Azure AD Connect on Windows Server. Use these modules to get current sync settings and force sync.
List the current AD sync settings:
Get-ADSyncScheduler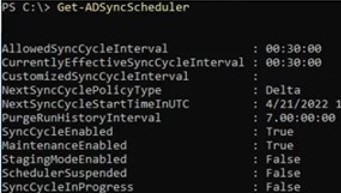
AllowedSyncCycleInterval : 00:30:00
CurrentlyEffectiveSyncCycleInterval : 00:30:00
CustomizedSyncCycleInterval :
NextSyncCyclePolicyType : Delta
NextSyncCycleStartTimeInUTC : 12/22/2022 11:45:50 AM
PurgeRunHistoryInterval : 7.00:00:00
SyncCycleEnabled : True
MaintenanceEnabled : True
StagingModeEnabled : False
SchedulerSuspended : False
SyncCycleInProgress : False
By default, data is synchronized from on-premises AD to AAD every 30 minutes (AllowedSyncCycleInterval ). You can set a custom sync interval using the CustomizedSyncCycleInterval parameter.
SyncCycleEnabled = False indicates that sync is temporarily disabled. You can enable it with the command:
Set-ADSyncScheduler -SyncCycleEnabled $trueTo force a delta sync to AAD (changes only), run the command:
Start-ADSyncSyncCycle -PolicyType DeltaThis will only affect the directory synchronization schedule. PHS synchronization is performed separately from directory synchronization.
Azure AD Connect Password Sync Warning: No Recent Synchronization
In my case, the following warning appeared on the Azure Portal:
Azure AD Connect
Password sync: no recent synchronization
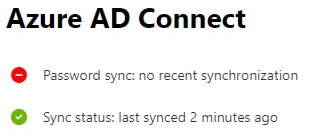
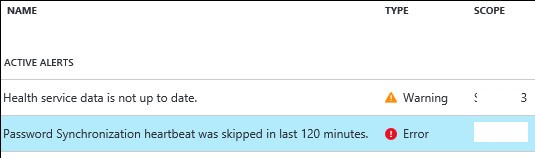
This alert also can be displayed in Azure AD:
Password Hash Synchronization heartbeat was skipped in last 120 minutes
The issue occurred after the Windows Server host with the Azure AD Connect role was shutdown for several hours during an infrastructure downtime. Synchronization of user attributes from the on-prem AD to Azure worked fine, but password hash sync stopped working.
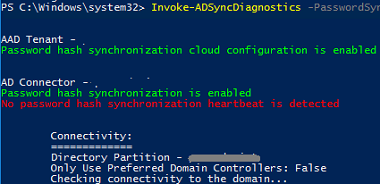
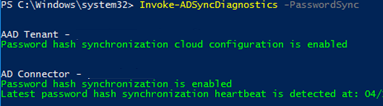
You can use the Invoke-ADSyncDiagnostics command to troubleshoot Azure AD connect password synchronization issues:
Import-Module ADSyncDiagnostics
Invoke-ADSyncDiagnostics -PasswordSyncIn our case, the command returned:
Password hash synchronization cloud configuration is enabled.
Password hash synchronization is enabled.
No password hash synchronization heartbeat is detected.
According to Microsoft documentation, each connector has its own password synchronization channel. If the password synchronization channel is established, but the connector doesn’t need to sync password changes (passwords in the on-premises AD DS have not been updated), then a heartbeat event with EventID 654 will be generated in the Application event log every 30 minutes:
Provision credentials ping end.
If there are no such events in the last three hours after running Invoke-ADSyncDiagnostics, an error will be returned. Event IDs 611 or 657 are also displayed in the Event Viewer when password synchronization errors occur.
- 611:
Password hash synchronization failed for domain: poweradm.com - 657:
Password Change Result - Anchor : B0H+OD3LM0GEnYODwdPhpg==, Result : failed, Extended Error
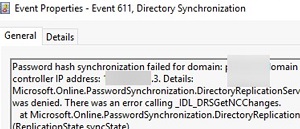
Microsoft.Online.PasswordSynchronization.DirectoryReplicationServices.DrsException: RPC Error 8453 : Replication access was denied. There was an error calling _IDL_DRSGetNCChanges.
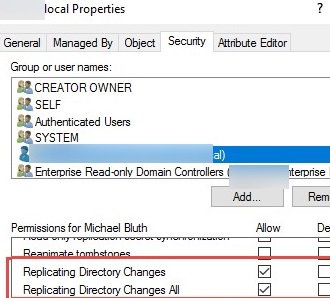
In this case, check that your AAD Sync user has the following permissions on the local ADDS domain root:
- Replicating Directory Changes: Allow
- Replicating Directory Changes All: Allow
It is possible that the Invoke-ADSyncDiagnostics command will return an error:
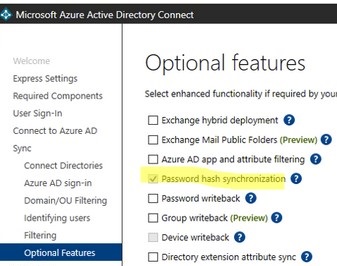
AAD Tenant: Password hash synchronization cloud configuration is disabled.
AD Connector: Password hash synchronization is disabled for all AD Connectors.
In order to synchronize passwords, you need to enable password synchronization from AADConnect wizard.
In this case, run the AzureADConnect wizard and enable the Password hash synchronization option under Sync -> Optional features.
Then check that the Azure AD Sync Scheduler job appears in the Task Scheduler. It must be enabled.
If the password hash does not synchronize for only one user, use the command to troubleshoot the problem:
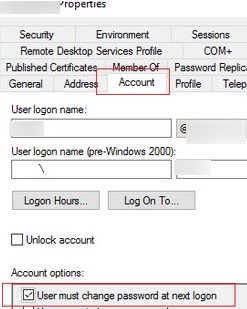
Invoke-ADSyncDiagnostics -PasswordSync -ADConnectorName "poweradm.com" -DistinguishedName "CN=TestUser,OU=Users,DC=poweradm,DC=com"If the User must change password at next logon option is enabled in the account properties in AD, this will also prevent password synchronization.
The fact that temporary passwords are not synchronized with Azure AD. You can use the following command to enable temporary password synchronization:
Set-ADSyncAADCompanyFeature -ForcePasswordChangeOnLogOn $trueHow to Force a Full Password Sync with Azure AD Connect?
Consider a PowerShell script to schedule a full password synchronization via Azure AD sync.
To find out the names of the connectors in your domain, run the command
Get-ADSyncConnector | Select Type,NameType Name
---- ----
Extensible2 poweradm.onmicrosoft.com - AAD
AD poweradm.local
If there is no heartbeat, you need to perform a full sync of all passwords using the following PowerShell script. Just replace the values of the $adConnector and $aadConnector variables (case sensitive!) with the names of your connectors.
Import-Module adsync
$adConnector = "poweradm.local"
$aadConnector = "poweradm.onmicrosoft.com - AAD"
$c = Get-ADSyncConnector -Name $adConnector
$p = New-Object Microsoft.IdentityManagement.PowerShell.
ObjectModel.ConfigurationParameter `
"Microsoft.Synchronize.ForceFullPasswordSync", `
String, ConnectorGlobal, $null, $null, $null
$p.Value = 1
$c.GlobalParameters.Remove($p.Name)
$c.GlobalParameters.Add($p)
$c = Add-ADSyncConnector -Connector $c
# Disable password sync through Azure AD Connect
Set-ADSyncAADPasswordSyncConfiguration `
-SourceConnector $adConnector `
-TargetConnector $aadConnector -Enable $false
# Enable synchronization and run the full password hash sync
Set-ADSyncAADPasswordSyncConfiguration `
-SourceConnector $adConnector `
-TargetConnector $aadConnector -Enable $true
After executing the script, the following message should appear:
Password Hash Sync Configuration for source "yourdomain" updated.
Wait a moment and run the command again:
Invoke-ADSyncDiagnosticsThe following message should appear:
The latest password hash synchronization heartbeat is detected at xx/xx/xx
If you then run the Invoke-ADSyncDiagnostics, the result will be as follows:
You should also see a message in the Azure portal (or in the Microsoft 365 Admin Center) that your password sync is now working:
Password sync: recent synchronization