In this article, we’ll look at how to protect the Linux GRUB2 bootloader configuration with a password.
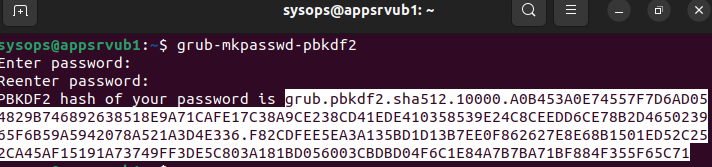
Generate a password hash using the grub-mkpasswd-pbkdf tool (available by default on Ubuntu):
$ grub-mkpasswd-pbkdf2Enter the password and confirmation, then copy the hash (starts with grub.pbkdf2.sha512…).
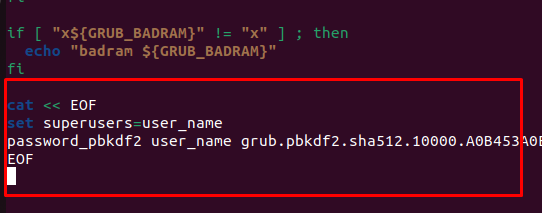
Edit the grub bootloader config file:
$ sudo nano /etc/grub.d/00_headerAdd the following lines at the end of the file:
cat << EOF
set superusers=user_name
password_pbkdf2 user_name password-hash
EOF
Update bootloader configuration:
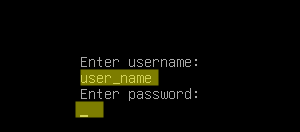
$ sudo update-grubReboot Linux:
$ rebootNow, when GRUB starts, a prompt will appear in which you need to enter a username and password. Without entering credentials, Linux will not boot.
Since the /etc/grub.d/00_header file contains a password hash, it is recommended to prevent it from being read and modified by anyone except the root user:
$ sudo chmod 711 /etc/grub.d/00_headerIn this mode, the GRUB password will be requested each time Linux boots. If you only want to protect the bootloader configuration from changes, edit the /etc/grub.d/10_linux file:
$ sudo nano /etc/grub.d/10_linuxFind the line:
CLASS="--class gnu-linux --class gnu --class os"
And add the –unrestricted option:
CLASS="--class gnu-linux --class gnu --class os --unrestricted"
Save the file and update the GRUB config:
$ sudo update-grub
I’ve followed your tutorial and when I add the unrestricted option to the indicated line, the GRUB menu with the different options disappears and there is no chance to enter pressing any key. The system starts the Ubuntu server automatically.
Thank you!
Nice tutorial.
Work for me on debian 11 and debian 12.