In this example, we’ll look at how to edit Linux configuration files with Ansible using sshd_config as an example. Our Ansible playbook should modify the sshd_config file and change/remove directives with insecure authentication algorithms.
We assume that you have already installed Ansible and created an inventory file. In the previous article, we showed you how to create a user and copy ssh keys using Ansible.
The following is an example of a playbook that uses regular expressions to:
- Edit some directives in sshd_config
- Disable insecure authentication algorithms
- Adds keys, ciphers, and MAC
In this example, we are configuring the anscfg user. Replace it with your username.
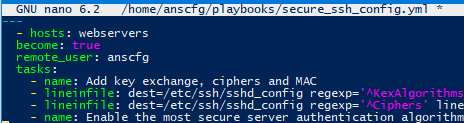
secure_ssh_config.yml
---
- hosts: webservers
become: true
remote_user: anscfg
tasks:
- name: Add key exchange, ciphers and MAC
- lineinfile: dest=/etc/ssh/sshd_config regexp='^KexAlgorithms' line='KexAlgorithms curve25519-sha256@libssh.org,diffie-hellman-group-exchange-sha256'
- lineinfile: dest=/etc/ssh/sshd_config regexp='^Ciphers' line='Ciphers chacha20-poly1305@openssh.com,aes256-gcm@openssh.com,aes128-gcm@openssh.com,aes256-ctr,aes192-ctr,aes128-ctr'
- name: Enable the most secure server authentication algorithms and protocol version 2
lineinfile: dest=/etc/ssh/sshd_config regexp='^Protocol 2' line='Protocol 2'
- lineinfile: dest=/etc/ssh/sshd_config regexp='^HostKey /etc/ssh/ssh_host_ed25519_key' line='HostKey /etc/ssh/ssh_host_ed25519_key'
- lineinfile: dest=/etc/ssh/sshd_config regexp='^HostKey /etc/ssh/ssh_host_rsa_key' line='HostKey /etc/ssh/ssh_host_rsa_key'
- name: Disable insecure algorithms
lineinfile:
dest: /etc/ssh/sshd_config
regexp: '^HostKey /etc/ssh/ssh_host_ecdsa_key'
state: absent
- lineinfile:
dest: /etc/ssh/sshd_config
regexp: '^HostKey /etc/ssh/ssh_host_dsa_key'
state: absent
- name: remove key files
file:
dest: /etc/ssh/ssh_host_ecdsa_key.pub
state: absent
- file:
dest: /etc/ssh/ssh_host_ecdsa_key
state: absent
- file:
dest: /etc/ssh/ssh_host_dsa_key.pub
state: absent
- file:
dest: /etc/ssh/ssh_host_dsa_key
state: absent
- name: Disable password login and allow login only with publickey.
lineinfile: dest=/etc/ssh/sshd_config regexp='^#?AuthenticationMethods' line='AuthenticationMethods publickey'
- lineinfile: dest=/etc/ssh/sshd_config regexp='^#?PasswordAuthentication' line='PasswordAuthentication no'
- lineinfile: dest=/etc/ssh/sshd_config regexp='^#?ChallengeResponseAuthentication' line='ChallengeResponseAuthentication no'
- lineinfile: dest=/etc/ssh/sshd_config regexp='^#?PubkeyAuthentication' line='PubkeyAuthentication yes'
# Set LogLevel to VERBOSE
- lineinfile: dest=/etc/ssh/sshd_config regexp='^LogLevel' line='LogLevel VERBOSE'
# Disable root login
- lineinfile: dest=/etc/ssh/sshd_config regexp='^PermitRootLogin' line='PermitRootLogin No'
# Allow only certain users to log in (you can specify AllowGroups)
- lineinfile: dest=/etc/ssh/sshd_config regexp='^AllowUsers' line='AllowUsers anscfg'
- name: restart sshd.
service:
name: sshd
state: restarted
- debug:
msg: "Ready! If necessary, generate client keys with the following command: ssh-keygen -t ed25519 -o -a 100 && ssh-keygen -t rsa -b 4096 -o -a 100"
If you get the error @ WARNING: REMOTE HOST IDENTIFICATION HAS CHANGED! when deploying such a playbook when connecting to remote hosts, remove the /home/user/.ssh/known_hosts file or delete the old keys and try connecting again.
