Best security practices for Windows domain networks recommend disabling local user accounts on computers and servers in an Active Directory domain. Local users who have administrative permissions on a computer can be a weak point in the security of your network. You can use tools such as Windows LAPS (Local Administrator Password Solution) to set unique, complex passwords for local administrators, or you can use AD Group Policies to completely disable local administrator and user accounts.
Disable the Built-in Local Administrator Account with Group Policy
There are several options in Group Policy to disable the built-in Windows Administrator account.
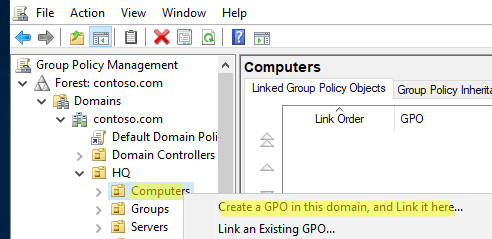
Open the Group Policy Management Console(gpmc.msc), create a new GPO and assign it to the OU (Organizational Unit) with the computers where you plan to disable local users (Create a GPO in this domain and Link it here).
Consider how to disable only the built-in administrator account on Windows.
Give the policy a name, then right-click it and select Edit.
- Expand the following GPO section Computer Configuration -> Policies -> Windows Settings -> Security Settings -> Local Policies -> Security Options;
- Find the Accounts: Administrator account status parameter and change its value to Define this policy setting -> Disabled;
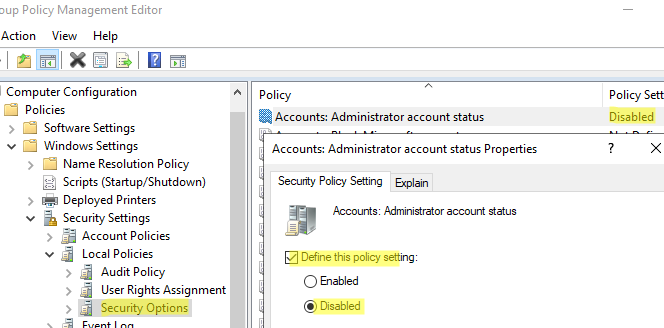
- Once the GPO has been updated on the target computer, the default administrator account will be disabled.
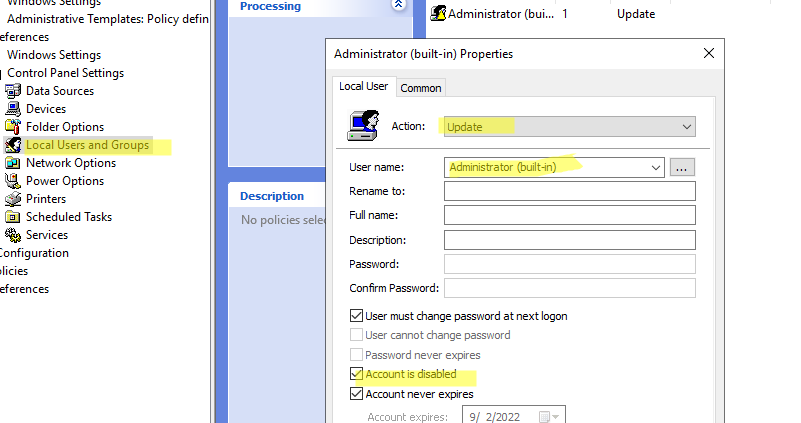
You also can disable the built-in administrator account on a Windows computer using the Group Policy Preferences:
- Go to the section Computer Configuration -> Preferences -> Control Panel Settings -> Local Users and Groups;
- Select New -> Local User;
- Create a new parameter with the following settings:
Action: Update
User name: Administrator (built-in)
Account is disables: True
To remove all local users from the built-in Administrators group, create a new setting in the same GPO section (New->Local Group).
Action: Update
Group Name: Administrators (built-in)
Delete all member users: True
Delete all member groups: True
Add: Add a domain security group here to which you want to grant the local administrator permissions on this computer (for technical support, HelpDesk or system administrators) -> Add to this group.
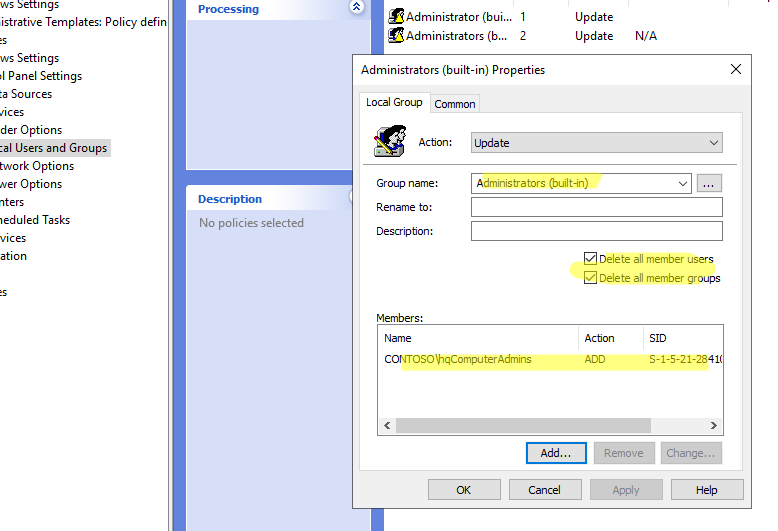
This policy removes any local or domain users that have been manually added to the Administrators group on the computer.
How to Disable Local Users with PowerShell
The built-in Microsoft.PowerShell.LocalAccounts module is available for managing local users and groups in Windows PowerShell 5.1 and later (installed by default on all versions of Windows starting with 8.1/Server 2012R2).
To view a list of local accounts on a computer, open the PowerShell console and run the command
Get-LocalUser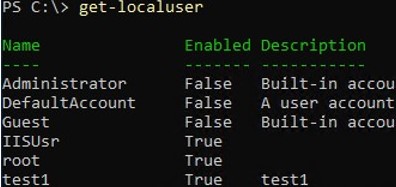
As you can see, there are several local users on the computer, some of which are disabled (Enabled=False).
To disable a specific local user, use the command:
Disable-LocalUser test1If you want to disable all local users, run the following PowerShell one-liner:
Get-Localuser| Disable-LocalUserOften, the administrator needs to disable all local users except for specific accounts.
For example, your task is to disable all local users with local Windows administrator permissions. To do this, you need to get a list of users in the local Administrators group (the well-known SID of this group is S-1-5-32-544) and disable all local users (PrincipalSource = Local).
$AdminGroupMembers = Get-LocalGroupMember -SID S-1-5-32-544 | Where-Object { $_.PrincipalSource -eq "Local" -and $_.ObjectClass -eq "User" }
foreach ($Member in $AdminGroupMembers) {
$Username= $Member.Name | Split-Path -Leaf
Disable-LocalUser $Username
}Use the following PowerShell script to disable all local users except those on the exclusion list:
$Exceptions = @("administrator", "root", "User3")
Get-LocalUser | Where-Object { $_.Enabled -eq $true -and $_.Name -notin $Exceptions } | ForEach-Object {
Disable-LocalUser $_
}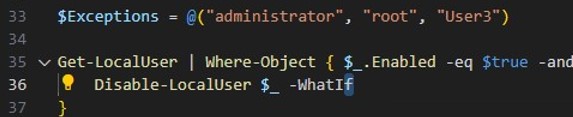
In this example, the PowerShell script disables all local user accounts on the computer except administrator, root, and User3.
Disable Local User Accounts on Domain Computers via Group Policy
There are no built-in settings in Windows GPO to disable all or only specific local users in Windows. So to disable all (or some) local users, you must use the startup script in the GPO.
Earlier, we looked at two examples of PowerShell scripts. One that disables all local users with administrator privileges. The other disables all users except those on the exclusion list.
- Save the PowerShell code to a
disable_local_user.ps1in the NETLOGON directory on the domain controller (for example\\contoso.com\netlogon). Check the NTFS permissions of the PS1 file. The Domain Computers group and/or the Authenticated Users group must have the Read and Execute permissions for the PowerShell script file; - Now create a new domain GPO and link it to the OU containing the computer objects;
- Edit your GPO;
- To run your PowerShell script when the computer starts, go to the GPO section Computer Configuration -> Policies -> Windows Settings -> Scripts (Startup / Shutdown) -> Startup. Switch to the PowerShell Scripts tab and add your PS1 file by specifying the UNC path to it in the NETLOGON folder;
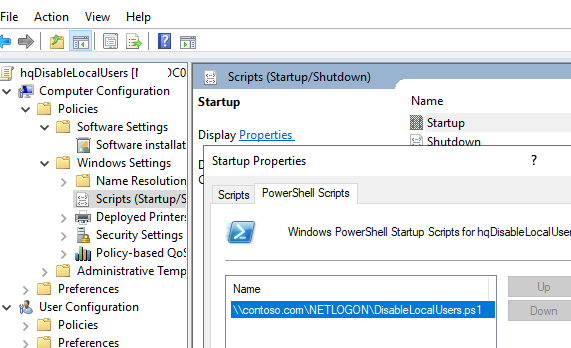
- Now the Group Policy client service will run your PowerShell script on a computer, which will disable all local users in Windows at startup.
