Several times I came across a situation where one of the users on a Windows Server host with an RDS (Remote Desktop Services) role ran an application that leaked and occupied all available RAM. It was impossible to connect to such a host via RDP remotely. To kill the leaked process, you need to remotely logoff this user.
Syntax of logoff.exe command:
logoff /server:<servername> <session ID> /vThe logoff command accepts the ID of the user session to end the session. To get a list of active user sessions on a remote computer, run the command:
quser /server:RemoteComputerNameUSERNAME SESSIONNAME ID STATE IDLE TIME LOGON TIME
admin console 1 Active none 1/5/2023 1:03 PM
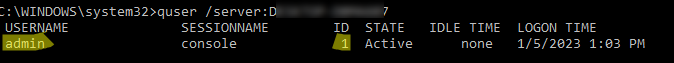
In this case, the admin user logs in locally (to the computer’s console). Its session id is 1.
You can get the session ID of a specific user:
quser /server:RemoteComputerName j.smith<rdp-tcp#X will be specified in the SESSIONNAME column. You can remotely force logoff a user’s session by its session ID. Run the command:
logoff 1 /SERVER:RemoteComputerName /vLogging off session ID 1
When a user session ends, all of its running processes will be killed. Check that there are no active sessions left on the remote computer:
quser /server:RemoteComputerNameNo User exists for *
You can use a small BAT script to logoff all active and disconnected user sessions on multiple terminal (RDS) hosts:
@echo off
setlocal
set servers=IST-RDS1 IST-RDS2
for %%s in (%servers%) do (
qwinsta /server:%%s | for /f "tokens=3" %%i in ('findstr /I "%username%"') do logoff /server:%%s %%i /v
)
You can also use the built-in rwinsta command to reset a user session remotely:
rwinsta rdp-tcp#12 /server:IST-RDS2or
rwinsta 22 /server:IST-RDS2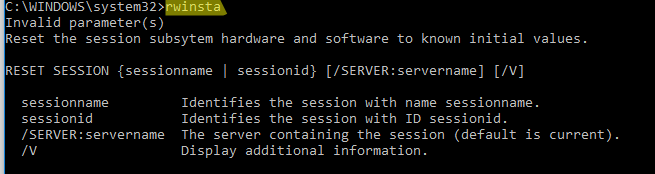
You can grant non-admin users permission to logoff/disconnect RDS user sessions using the command:
wmic /namespace:\\root\CIMV2\TerminalServices PATH Win32_TSPermissionsSetting WHERE (TerminalName ="RDP-Tcp") CALL AddAccount "domain\group",2