By default, OpenVPN certificates are used to authenticate users. This means, that any user who has a *.ovpn file with connection settings and certificates can connect to your OpenVPN server. In OpenVPN, you can enable and configure user authentication through an LDAP server (Active Directory or FreeIPA).
Let’s look at two scenarios for connecting to an LDAP server to validate user credentials:
- openvpn-auth-ldap plugin
- external scripts
Configuring Active Directory Authentication Openvpn-auth-ldap plugin
Install the openvpn-auth-ldap package on the OpenVPN server. For example, on Ubuntu/Debian, you can install the plugin with the command:
# apt-get install openvpn-auth-ldap –yMake changes to the server.conf file:
# nano /etc/openvpn/server.confusername-as-common-name
plugin /usr/lib/openvpn/openvpn-auth-ldap.so /etc/openvpn/auth/ldap.conf
Create a new user in Active Directory openvpnsvc with password 02en1VPpas. The OpenVPN server will use this account to access LDAP.
Then create the domain security group VPN_users. Add user accounts to it that are allowed to authenticate via OpenVPN.
Now create the /etc/openvpn/auth directory and the ldap.conf file:
# mkdir /etc/openvpn/auth && nano /etc/openvpn/auth/ldap.confURL ldap://ln-dc01.poweradm.com
BindDN CN=openvpnsvc,CN=Users,DC=poweradm,DC=com
Password 02en1VPpas
Timeout 15
TLSEnable no
BaseDN "DC=poweradm,DC=com"
SearchFilter "(&(sAMAccountName=%u)(memberOf=CN=VPN_ users,CN=Users,DC=poweradm,DC=com))"
Note. Change the LDAP connection settings to your DC and DNs in the file.
Restart openvpn:
# service openvpn restartAdd the following line to the .ovpn configuration file on the clients:
auth-user-pass
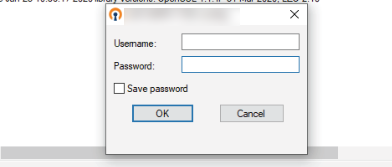
You will now be prompted for your AD user credentials when connecting to the OpenVPN server.
Active Directory Authentication for Windows OpenVPN Server
If you are running an OpenVPN server on Windows, you won’t be able to install the openvpn-auth-ldap plugin on it. In this case, a set of BAT/VBS scripts can be used to authenticate OpenVPN users via Active Directory.
We assume that you have created a VPN_users group in AD and added users to it who are allowed to connect to OpenVPN.
On the OpenVPN server, add the following parameters to the server.conf file:
script-security 3
auth-user-pass-verify OpenVPNAuthWrapper.cmd via-env
Now create the following files in the directory with the server.conf config file:
- auth4openvpn.ini
- Auth4OpenVPN.vbs
- AuthOpenVPNWrapper.cmd
auth4openvpn.ini
Server = "192.168.10.100"
Domain = "POWERADM"
DN = "OU=Users,DC=poweradm,DC=com"
Group = "VPN_users"
Logging = "On"
Auth4OpenVPN.vbs file code is available here https://sites.google.com/site/amigo4life2/openvpn
AuthOpenVPNWrapper.cmd
set LOCALAPPDATA=C:\Users\%USERNAME%\AppData\Local
set CommonProgramFiles=C:\Program Files\Common Files
set CommonProgramFiles(x86)=C:\Program Files (x86)\Common Files
set CommonProgramW6432=C:\Program Files\Common Files
C:\Windows\System32\cscript.exe "C:\Program Files\OpenVPN\config\Auth4OpenVPN.vbs"
exit %errorlevel%Restart OpenVPNService using PowerShell command:
Get-Service OpenVPNService| Restart-ServiceAdd the following lines to the *.ovpn client configuration file:
auth-user-pass
auth-retry interact
Your Windows OpenVPN server can now validate the user’s credentials against Active Directory.

Your link to the Auth4OpenVPN.vbs file is not working, are you able to provide a copy of this code?